InsightVM
A vulnerability management tool that allows you to detect, mitigate, and report on security vulnerabilities found in systems and software.
Overview
InsightVM scan tool is a commercial network-based application used to scan systems for technical vulnerabilities. The scanner actively probes for vulnerabilities using a multi-level scan with a large database of known security holes to identify common system vulnerabilities many of which are caused by oversights such as misconfiguration or missing patches.
Many of the vulnerabilities are also included in CERT, CIAC, and SANS security organization advisories. New checks for vulnerabilities are added continuously to the scanner.
Highlights
Vulnerability scanning is only allowed for systems for which you are specifically authorized (e.g., your unit if that is your responsibility). University Information Security is the only unit authorized to scan throughout the University of Minnesota network.
Scans and reporting are self-managed by University units. The process includes:
- Schedule discovery scan -- schedule weekly to Identify systems in the IP ranges units manage.
- Maintain list of IP addresses -- identify systems by IP address either individually or group into asset groups for vulnerability management.
- Schedule vulnerability scan -- schedule at least weekly for systems in your unit.
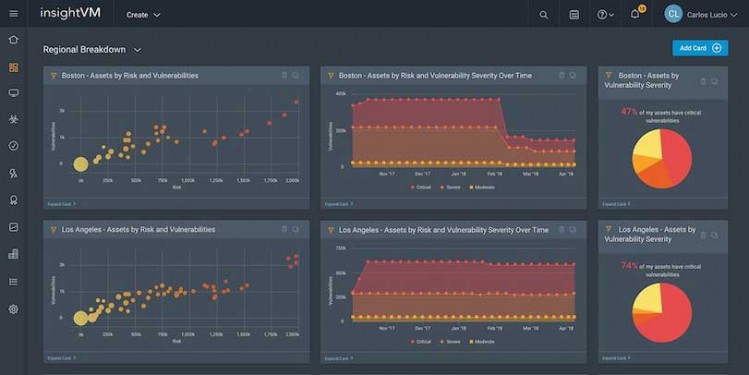
- Review results -- use dashboards and reports.
- Remediate vulnerabilities detected -- prioritize and fix high-severity vulnerabilities or document why the vulnerability cannot be fixed or does not pertain. Remediate other vulnerabilities.
- Re-scan if necessary -- schedule re-scans to determine if the vulnerabilities have been fixed.
- Use remediation requests -- document false positives and remediation fixes that require more time to fix.
- View dashboards and run reports -- use various report templates and asset views to produce dashboards and reports to meet your vulnerability management needs.
See the University Technical Vulnerability Management standard in the Information Security Policy for current requirements on frequency of vulnerability scanning, type of vulnerability scan, remediation timeframes, and reporting.
University Information Security coordinates the external vulnerability scan for systems and network devices that are in scope for the credit card data environment (CDE). These scans meet the Payment Card Industry (PCI) Scanning (PDF) requirement. See Manage External Vulnerability Scans for PCI DSS.
Getting Started
For UMN InsightVM users, see Manage Scans (authentication required).
Reminder: User and API access is unavailable during the scheduled maintenance window on Thursdays 6 a.m. to 12 p.m. (noon).
Intended Audience
Cost
University-funded: no charge.